Keeping pace with cybersecurity threats reveals the quickest way to identify your network’s weakest entry point—discover the essential strategies to stay ahead.
Browsing Tag
Cybersecurity
30 posts
If You Use Smart Plugs, This Firmware Risk Is Everywhere
When using smart plugs, firmware vulnerabilities pose widespread risks that could compromise your security—discover how to protect your smart home today.
Securing Home Automation Hubs Against Ransomware
In protecting your home automation hub from ransomware, understanding key security measures can make all the difference—discover how to stay secure.
The “Local API” Feature Is Great—Until You Leave It Exposed
An exposed Local API can pose serious security risks, making it crucial to understand how to protect your device from potential threats.
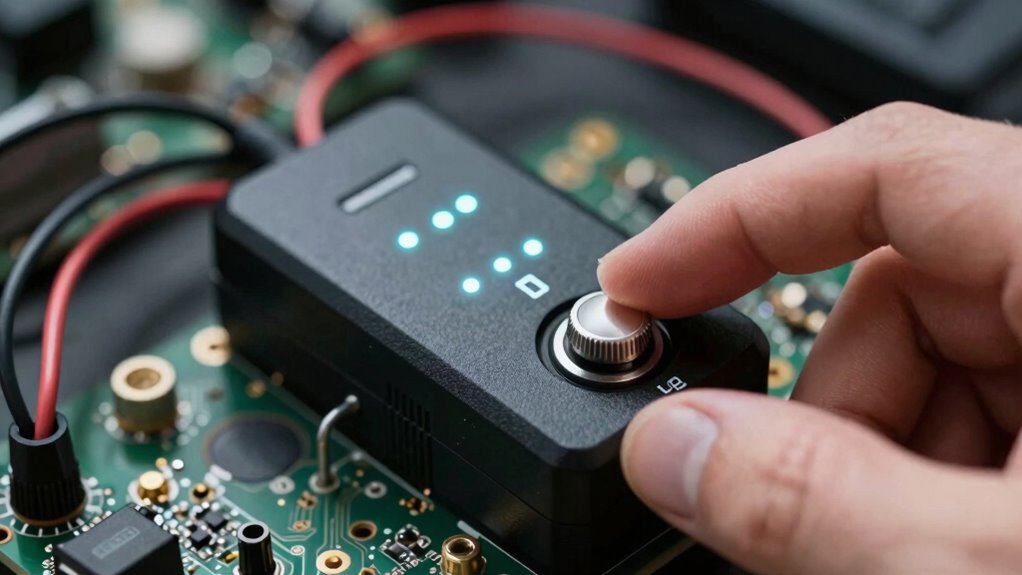
How to Build a “Kill Switch” for Compromised Devices
Create a reliable kill switch for compromised devices by following essential steps to ensure maximum security and quick response when threats arise.
The “Time Spoofing” Attack That Can Break Automations
Beware of time spoofing attacks that can disrupt your automations and security—discover how this hidden threat can compromise your systems.
Shared Users Can Be a Risk—Set Ring Permissions the Safe Way
Discover why shared user accounts pose security risks and learn safe ring permission strategies to protect your system from potential threats.
Your Alarm’s Installer Code Is Still Default—Fix It Before Someone Uses It
Optimize your home security now—discover how to change your alarm’s default installer code before it’s exploited.
Local Storage vs Cloud Storage for Security Cameras: What to Know
Understanding the differences between local and cloud storage for security cameras helps you choose the best option—find out which is right for your security needs.
Are Smart Locks Vulnerable to Man‑in‑the‑Middle Attacks?
What makes smart locks vulnerable to man-in-the-middle attacks, and how can you safeguard your device from hidden security risks?