To protect your privacy, stop granting unnecessary permissions to your smart-home apps. Avoid giving access to location, microphone, camera, contacts, or personal data unless absolutely needed. Regularly review and revoke permissions you no longer use or trust. Keep your device settings updated to tighten control. Being cautious with these permissions prevents potential security risks and data breaches. Stay informed on how to manage app permissions effectively to keep your smart home safe and private.
Key Takeaways
- Regularly review and revoke unnecessary permissions in your device settings.
- Limit app access to sensitive data like microphone, camera, location, and contacts.
- Only grant permissions that are essential for the app’s core functions.
- Avoid allowing continuous background access to prevent potential misuse or surveillance.
- Keep your smart-home apps and device firmware updated to enhance security and control.

WeHere 32-Key Plus Key Lock Box Wall Mount – Commercial Smart Key Cabinet with App, Keypad, Bluetooth & WiFi Unlock (Sold Separately), Key Management System Access Log Tracking for School, Office
Commercial Key Management for Office & Rental Use – Designed for small businesses, rental properties and facility management,…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
What Are Smart-Home App Permissions and Why Do They Matter?

Smart-home app permissions are the tools that determine what data and functions your smart devices can access and control. They guarantee your devices work smoothly by verifying device compatibility and establishing trusted connections. User authentication is a key part of this process, confirming that only authorized users can access or modify your smart home setup. When permissions are granted, they define the level of control the app has, such as adjusting thermostats or opening doors. Proper permissions prevent unauthorized access, keeping your smart home secure. However, granting overly broad permissions can expose your devices to risks. Knowing what permissions your apps request helps you make smarter choices about privacy and security, guaranteeing your smart home remains safe and functions efficiently. Understanding the affiliate disclosure and privacy policies associated with your smart-home apps can also help you stay informed about how your data is used. Paying attention to permissions management can further enhance your control over your device security. Being aware of permission scope helps you understand the extent of access granted to each app, reducing potential vulnerabilities. Additionally, familiarizing yourself with security best practices can significantly improve your overall smart-home security posture.

GNCC 2K Security Cameras 4pcs, Home Security Camera Indoor with 360° Motion Detection for Pets/Baby/Dog, Two-Way Audio, Night Vision, 24/7 SD Card Storage, Cloud Storage, Compatible with Alexa
【2K & Night Vision】: GNCC Security Camera Indoor comes with 2K FHD quality video and images. You can…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
How Overly Invasive Permissions Can Threaten Your Privacy

When apps request more permissions than necessary, they can secretly access sensitive information about you and your habits. This poses serious privacy implications, as your personal data—like routines and preferences—may be exposed or misused. Overly invasive permissions can give apps access to details beyond their intended function, increasing the risk of data breaches or misuse. To protect yourself, follow permission best practices: only grant permissions that are essential for the app’s core features, and regularly review and revoke unnecessary access. Being cautious about permissions helps limit the information apps can collect, reducing privacy risks. Vetted permissions policies ensure you understand what data is being accessed and how it’s used. Understanding permission management and related concepts can help you better evaluate the necessity of app permissions. Additionally, staying informed about privacy settings can help you customize your app permissions more effectively. Remember, granting fewer permissions keeps your data safer and maintains better control over your personal information. Regularly reviewing security protocols can further strengthen your privacy defenses.
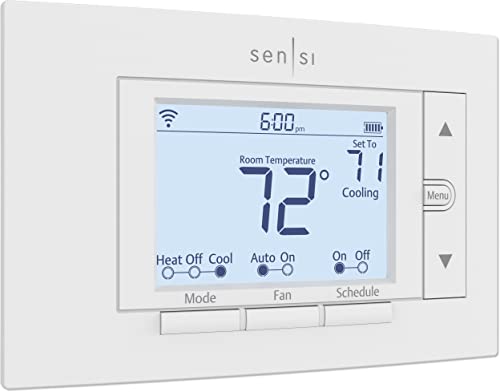
Emerson Sensi Wi-Fi Smart Thermostat for Smart Home, DIY, Works With Alexa, Energy Star Certified, ST55
PRIVACY PROTECTION*: Sensi won’t sell your personal information to third parties
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Why Location, Microphone, and Camera Access Are Risky?

Have you ever considered how granting access to your location, microphone, or camera can put your privacy at risk? These permissions can reveal sensitive details about your daily routines and personal environment. When you enable voice control or device integration, you’re often giving apps permission to listen or watch constantly, even when you don’t realize it. This can lead to misuse or hacking. Unsecured device connections can create vulnerabilities that malicious actors may exploit. Additionally, device security best practices are crucial to minimize these risks and protect your personal information. Implementing encryption protocols can further safeguard your data during transmission.
- Unauthorized recording of your conversations
- Tracking your location without consent
- Eavesdropping through your microphone
- Spying via your camera in private moments
- Data leaks from poorly secured device connections
- Secure device connections are essential to prevent unauthorized access and safeguard your data.
Being cautious with these permissions helps protect your privacy and keeps your smart home secure. Always evaluate if the access is truly necessary for the app’s function.

eufy Security Smart Lock C220, Fingerprint Keyless Entry Door Lock, Built-in Wi-Fi, App Remote Control, Front Door Smart Lock Deadbolt, 8Months Battery, Reliable Power, IP53 Waterproof, BHMA Grade 3
8 Months Battery Life: With 8 AA batteries, Smart Lock C220 runs around 8 months. Experience ultimate convenience…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Do You Really Need Access to Contacts and Personal Data?

Granting apps access to your contacts and personal data often seems harmless, but it can expose sensitive information that you might not realize is at risk. Many smart-home apps ask for this data unnecessarily, raising privacy concerns and creating vulnerabilities. Sharing personal details can lead to privacy breaches or misuse of your information, especially if the app’s data security isn’t solid. Before granting access, ask whether the app truly needs this information to function. If it doesn’t, refuse permission. Protecting your privacy means being cautious about what you share. Limiting access minimizes potential data security risks and keeps your personal information safe from exploitation, identity theft, or unwarranted tracking. Always evaluate if the benefits outweigh the privacy concerns before giving an app access to your contacts and personal data. Being aware of privacy risks can help you make smarter decisions about your digital safety, especially when you consider the security measures the app employs to protect your data. Additionally, understanding the importance of data security can guide you in choosing apps that prioritize user privacy. Recognizing vulnerabilities in app permissions can further help you safeguard your personal information. To enhance your understanding, stay informed about common privacy breaches associated with smart-home technology.
Simple Steps to Review and Revoke Unnecessary Permissions

Taking a few minutes to review and revoke unnecessary app permissions can substantially boost your privacy. Proper permission management reduces privacy risks and prevents apps from accessing more data than needed. Start by checking your device’s app settings, and look for permissions related to location, camera, microphone, and contacts. Be aware that some permissions, like those associated with wave and wind data, can impact how apps function and share information. Additionally, understanding the role of air quality data in smart-home devices can help you make informed decisions about granting permissions. Recognizing sensor data, a critical element in smart home privacy, can guide you in managing app access more effectively. Regularly reviewing permission scopes helps ensure that apps only access necessary information, further strengthening your privacy. Here are simple steps to improve permission management:
Taking a few moments to review app permissions can greatly enhance your privacy and security.
- Review app permissions regularly in your device settings
- Revoke access for apps that don’t need certain permissions
- Limit permissions for smart-home apps to essentials only
- Use app-specific permission settings to fine-tune access
- Keep your device and apps updated for better control and security
Frequently Asked Questions
Can Granting Permissions Lead to Unauthorized Device Control?
Yes, granting permissions can lead to unauthorized device control. When you give apps access, they might respond to voice commands unexpectedly or share your data without permission. This can compromise your privacy and security. Always review app permissions carefully, and limit access to only what’s necessary. Protect yourself by being cautious about what you allow, especially with smart-home apps that can control your devices through voice commands and data sharing.
Are Permissions Different Across Various Smart-Home Platforms?
Permissions vary across different smart-home platforms due to platform-specific privacy policies and security standards. You’ll notice permission inconsistencies, as some platforms restrict access tightly while others are more permissive. It’s important to review each platform’s privacy settings carefully, so you can control what devices and apps can access. This way, you protect your smart home from potential vulnerabilities caused by overly broad or inconsistent permissions.
How Often Should I Review App Permissions?
You should review your app permissions at least once every three months. Studies show that over 60% of users don’t regularly check privacy settings, increasing security risks. Regular permission management helps protect your smart home from potential privacy concerns by ensuring apps only access what’s necessary. Stay proactive, and review permissions more frequently if you notice unusual app behavior, new app updates, or if your security needs change.
What Signs Indicate a Smart-Home App Is Malicious?
You can tell a smart-home app is malicious if it requests unnecessary permissions or shows signs of permission escalation, which threaten your device security. Watch for unusual behavior, like unexpected device control or data access. If an app asks for access beyond its function, it’s a red flag. Regularly reviewing permissions helps prevent malicious activities, ensuring your smart-home system stays safe and secure from potential threats.
Do Permissions Affect the App’s Update Process?
Did you know that 85% of users don’t realize permissions can influence app security? Permissions do affect the app’s update process since permission updates are often required for new features or security improvements. If you deny permissions, it might block updates, leaving your smart-home app vulnerable. Always review permission requests during updates to guarantee your app remains secure and fully functional, protecting your devices and personal data.
Conclusion
Remember, a little caution goes a long way—trust, but verify. Regularly review your smart-home app permissions and revoke anything that seems unnecessary. Don’t assume all permissions are harmless; some can put your privacy at risk. By staying vigilant and controlling what apps can access, you protect yourself from potential breaches. As the saying goes, “An ounce of prevention is worth a pound of cure.” Stay smart and keep your home safe.








