To audit your alarm event history for suspicious patterns, you should first review logs to identify unusual spikes, repeated triggers outside normal hours, or anomalies in access attempts. Use filtering tools to focus on relevant alarms and look for connections between events that suggest coordinated threats. Continuously monitor and update your alarm settings to catch emerging patterns. Staying vigilant helps recognize signs of breach early—exploring further can give you even more effective detection strategies.
Key Takeaways
- Review alarm timestamps to identify unusual activity outside normal hours or repeated triggers.
- Analyze alarm thresholds and patterns to detect spikes or frequent false alarms indicating potential threats.
- Correlate related events across logs, such as login attempts and access points, for signs of coordinated attacks.
- Use filtering and categorization tools to focus on relevant alarms and reduce data noise during audits.
- Continuously update alarm settings and employ automated monitoring to promptly detect and respond to suspicious patterns.

AILITRON BM6 Bluetooth 12V Battery Monitor & Load Tester – Wireless Alternator & Charging System Analyzer for Lead-Acid & Lithium Batteries, 30-Day Auto Trip Record, App Alarm, IP67 Waterproof
[2026 UPGRADED: MANAGE 4 BATTERIES AT ONCE] Stay ahead with our exclusive multi-battery dashboard, allowing you to monitor…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
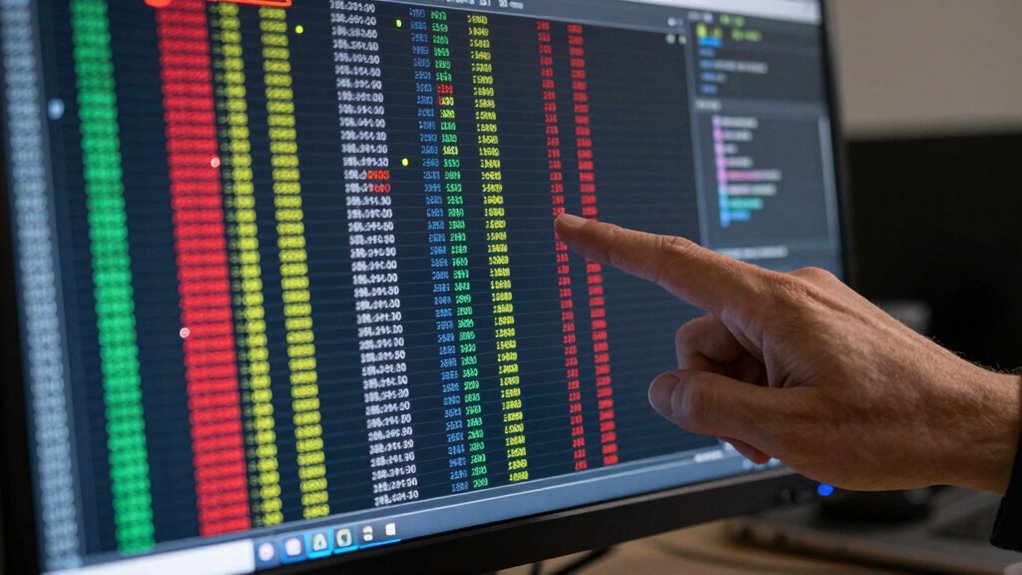
Interpreting Your Alarm Event Data
Understanding your alarm event data is essential for effective security management. It helps you identify which alarms need immediate attention through alarm prioritization, ensuring critical issues are addressed promptly. When reviewing your alarm logs, pay close attention to event timestamping; accurate timestamps allow you to track the sequence of events and detect patterns over time. Proper interpretation of this data enables you to distinguish between false alarms and genuine threats. By analyzing how alarms are prioritized and when they occur, you can refine your response protocols and improve overall security efficiency. Remember, clear and precise alarm data is the foundation for making informed decisions, reducing response times, and strengthening your security system’s reliability. Additionally, understanding alarm system components can help you troubleshoot issues more effectively and maintain system integrity. Recognizing electric dirt bike horsepower can also guide you in assessing the severity of certain alarm events related to power or motor systems, especially in security environments with automated or motorized equipment. Being familiar with alarm event patterns can further aid in identifying potential security breaches before they escalate. Familiarity with alarm system diagnostics can streamline troubleshooting and reduce downtime, leading to more reliable security coverage.

Ring Alarm 8-Piece Kit (newest model), Home or business security system with optional 24/7 professional monitoring
A great fit for 1-2 bedroom homes, this kit includes one base station, one keypad, four contact sensors,…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Recognizing Suspicious Patterns in Alarm Logs

Recognizing suspicious patterns in alarm logs is crucial for differentiating genuine security threats from false alarms. Pay attention to alarm thresholds; if you notice alarms triggered repeatedly or outside normal operating hours, it may indicate malicious activity. Unusual spikes in alarms, especially during times when staff shouldn’t be accessing certain areas, are red flags. Additionally, monitor user access patterns—if someone is repeatedly attempting to access restricted zones or triggering alarms beyond their typical activity, it warrants further investigation. Consistent, abnormal activity that deviates from established access routines can signal a security breach. Performing event log analysis can help identify these irregularities more efficiently. Reviewing alarm history in detail can uncover recurring issues or anomalies that might otherwise go unnoticed. Regularly reviewing your system capabilities and detection methods can help you stay informed about system features and enhancements, ensuring your security measures remain effective. By identifying these patterns early, you can respond promptly and prevent potential incidents, ensuring your home security systems remain effective and reliable.
alarm event log review tool
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Using Tools and Filters for Alarm Analysis

Analyzing alarm logs manually can be overwhelming, especially when dealing with large volumes of data. To streamline this process, use tools that enable effective alarm filtering and event categorization. These tools allow you to focus on relevant alarms, reducing noise and highlighting suspicious activity. Consider these key features: practical system design, which can help you develop more efficient alarm management strategies that suit your home’s needs, and understanding alarm event characteristics can improve your ability to identify patterns indicative of potential security issues. Incorporating automated analysis techniques, which leverage contrast ratio insights from projector technology to identify subtle anomalies, can further enhance your capacity to detect anomalies quickly and accurately, saving time and increasing detection reliability.

GRSICO 9-Piece Home Security System, WiFi Wireless Alarm System, 120dB Siren Alert, DIY Smart Security System for House and Apartment, Smart Life App Control, No Monthly Fee, 2.4GHz WiFi
DIY Home Alarm System – Easy Setup in Minutes: Protect your home right out of the box with…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Correlating Events to Detect Security Breaches

To effectively detect security breaches, you need to correlate related events across multiple alarm logs. This process, called event correlation, helps you identify patterns that indicate malicious activity rather than false alarms. By linking suspicious login attempts, unusual data transfers, and access to sensitive areas, you can uncover coordinated efforts that might go unnoticed individually. Event correlation reduces false alarms by filtering out benign activities and highlighting genuine threats. It allows you to see the bigger picture, making it easier to recognize complex attack strategies. When you analyze correlated events, you gain more accurate insights into potential breaches, enabling faster and more targeted responses. This approach is essential for distinguishing real threats from false alarms and strengthening your security posture. For example, Youngster Choice exemplifies how understanding individual behaviors can inform broader security assessments. Additionally, understanding event patterns can help in developing more effective detection rules and response plans. Recognizing threat indicators across logs further enhances your ability to proactively address security issues before they escalate, especially when combined with security analytics to interpret complex data. Incorporating correlation techniques can significantly improve your detection capabilities by revealing hidden relationships among seemingly unrelated events.
Setting Up Continuous Monitoring and Response

Setting up continuous monitoring and response is essential for maintaining your security posture in real-time. It ensures you detect and address suspicious patterns promptly. Start by optimizing your alarm configuration to filter false positives and prioritize critical alerts. Next, implement automated response protocols that trigger immediate actions when specific triggers occur. Finally, invest in staff training so your team can interpret alarm data accurately and respond effectively. Consider these steps:
- Regularly review and update alarm settings to adapt to evolving threats.
- Deploy real-time monitoring tools that integrate with your alarm system, utilizing advanced detection techniques to identify subtle anomalies.
- Conduct ongoing staff training sessions to enhance response efficiency and awareness.
- Incorporate alarm event analysis to identify recurring issues and refine your monitoring strategies. Additionally, understanding luxury security technology can help you select the most advanced systems to protect your assets effectively. Integrating smart security features can further enhance detection capabilities and streamline your response processes. Incorporating comprehensive data analysis can also help you uncover hidden patterns and improve your overall security strategy.
This structured approach guarantees that your security system remains vigilant, responsive, and capable of handling emerging risks proactively.
Frequently Asked Questions
How Often Should I Conduct Alarm Event Audits?
You should conduct alarm event audits at least monthly to maintain effective security. Adjust the audit frequency based on your alarm system’s alarm frequency—more frequent reviews are necessary if you experience frequent or suspicious alarms. Regular audits help you identify patterns, reduce false alarms, and guarantee your system’s integrity. Staying consistent with your audit schedule keeps you proactive and better prepared to respond to potential security threats.
What Are Common False Alarm Indicators?
False alarm indicators often include false alarm triggers caused by sensor malfunctions or environmental factors like pets, weather, or vibrations. You might notice repeated triggers without actual intrusion, or alerts from sensors that aren’t properly calibrated. These issues can lead to unnecessary alarms, so regularly checking your sensors for malfunctions and ensuring they’re correctly positioned helps reduce false alarms and keeps your security system reliable.
How Do I Prioritize Suspicious Patterns?
Like a seasoned detective in a noir film, you recognize that prioritizing suspicious patterns involves sharp pattern recognition and thorough risk assessment. Focus first on recurring events or anomalies that deviate from normal activity. Assign higher priority to patterns indicating potential security breaches, such as multiple alarms in a short span or unusual access times. By systematically evaluating these signals, you guarantee your response targets the most critical threats efficiently.
Can I Automate Alarm Analysis Completely?
Yes, you can automate alarm analysis completely using alarm correlation and data visualization tools. These systems automatically identify suspicious patterns by correlating alarm data across multiple sources, highlighting anomalies. Data visualization helps you quickly interpret complex information, making it easier to spot suspicious activity without manual effort. By integrating these technologies, you streamline your security monitoring, reduce false alarms, and guarantee a swift response to potential threats.
What Legal Considerations Exist for Alarm Log Reviews?
Reviewing alarm logs is like walking a tightrope—you need to stay balanced with legal considerations. You must guarantee privacy compliance by only accessing logs relevant to authorized personnel and safeguarding sensitive data. Keep thorough legal documentation of your review process to protect against liability. Always stay updated on local laws and regulations, as unauthorized access or mishandling alarm data can lead to legal trouble.
Conclusion
Regularly auditing your alarm event history is key to catching suspicious activities early. Did you know that 60% of security breaches are detected through event logs before any damage occurs? By understanding patterns, using the right tools, and setting up ongoing monitoring, you can markedly improve your security stance. Stay proactive, stay vigilant, and remember—your alarm logs are your first line of defense against potential threats.









